Important
This post is not a write-up. I won't share exploit code, reproduction steps, or technical details about the vulnerability. If you're looking for that, this is not the right place. What follows is a personal reflection on what it took to get here.
The CVE
On May 12, 2026, Apple published a security update crediting a sandbox escape I found in the App Intents framework. The research and the bug submission were done on macOS, even though the initial primitive also worked on iOS:
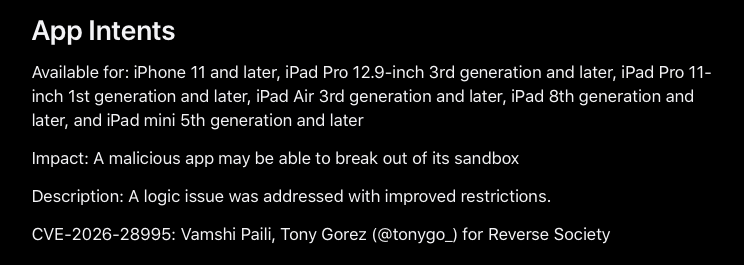
Source: Apple security update.
It's one line in a long list of patches. But for me, it represents months of work, frustration, and learning.
How it started
Everything started with Mickey Jin's research on macOS sandbox escapes. That post showed a class of vulnerabilities that felt approachable. Not kernel-level complexity, but still meaningful. I thought: maybe I can find one too.
So I started looking. And looking. And looking.
The process was incredibly tedious. Manually checking XPC services, reading entitlements, testing connections one by one. After a while, I started writing scripts to automate parts of it. Filtering services, checking which ones were alive, which ones accepted connections from sandboxed apps. I've shared some of that methodology before.
I also used the Binary Ninja MCP server to extract XPC interfaces faster and write proof-of-concept clients more quickly.
Automation helped, but it didn't find the bug for me. It just made the haystack smaller.
The gap between finding and understanding
At some point, I had something. A first version of the sandbox escape that worked, sort of. I could trigger a file write outside the sandbox and I had some control over the content, but I couldn't choose the file name, its extension, or where it would land.
This is something people rarely talk about. There's a big difference between finding a bug and proving its impact. Writing a file outside the sandbox is already something you should never be able to do. But to really demonstrate impact, you need to control the content, the location, the file name. That's what turns a bug into a vulnerability.
At first, I thought what I had was enough. I submitted the bug to Apple as it was and moved on.
Asking for help
I reached out to Gergely Kalman and Csaba Fitzl and shared a video showing what the exploit did. Their reaction was clear: no real impact. You can write a file outside the sandbox, sure, but you don't control enough to make it dangerous.
I explained what I had submitted to Apple and where I thought the limits were.
We worked together for about ten days. I had the first version of the exploit running. Gergely picked it up, tweaked it, pushed it a bit further. Then Csaba took over, modified the exploit again, and got it to work in a way none of us had managed before. We shared a single exploit and each of us added a piece of code that unlocked the next step. We didn't divide the work. We built on each other's progress.
After ten days we went from "a file appears somewhere it shouldn't" to "we can write a controlled file to a chosen location outside the sandbox." I wouldn't have gotten there alone.
What I learned
Finding a CVE didn't make me feel like an expert. I'd never even looked at App Intents before Mickey Jin's post made me curious. I found this bug because I try to be persistent and because I asked for help when I got stuck.
A few things I'll carry with me:
Automation gets you to the starting line, not the finish. Scripts can filter thousands of services down to a handful of candidates. But understanding why something is vulnerable requires reading code, thinking, and testing hypotheses manually.
The first version is never the final one. Having a crash or an unexpected behavior is not the same as having a vulnerability. The distance between the two is where the real learning happens.
Collaboration is not a weakness. Reaching out to Gergely and Csaba was the best decision I made in this process. They taught me how to think about the problem differently.
Thank you
To Mickey Jin for the research that started all of this. To Gergely Kalman and Csaba Fitzl for their time, patience, and expertise during those ten days. They also run a macOS security training if you want to learn from them directly. This was my first CVE. I hope it won't be the last.